Purple Team Simulation
Think Like Your Adversaries. Defend What Matters.
Overview
Today’s cyber threats are no longer theoretical. Attackers operate with patience, precision, and a clear understanding of how to exploit gaps across technology, process, and people. Traditional security assessments often identify vulnerabilities, but they do not always answer the questions executives and security leaders care about most:
Can we detect a real attack? Can we respond fast enough? Are we defending the systems that matter most to the business?
HolistiCyber’s Purple Team Service is designed to answer those questions.
A Purple Team exercise brings together offensive security expertise and defensive operations in a collaborative, controlled engagement. HolistiCyber simulates realistic attacker behavior while working side by side with the organization’s security team to validate detection, improve response, tune security tools, and strengthen operational readiness.
Unlike traditional red team engagements, where the offensive team operates quietly and presents findings at the end, HolistiCyber’s Purple Team approach is built around real-time learning, measurable improvement, and business-aligned defense.
HolistiCyber’s unique framework is based on three principles:
Simulate from the attacker’s point of view
Think like your adversaries
Prioritize and defend what matters
The result is a practical, high-impact service that helps organizations move from assumed security to validated security.
MITRE ATT&CK describes adversary tactics as the “why” behind attacker behavior and techniques as the “how” adversaries achieve their objectives. HolistiCyber uses this type of adversary behavior modeling to help organizations test and improve defenses against realistic attack paths, not generic checklists.
War Games - Cyber Style
23% monthly
17% quarterly
15% bi-annually
17% annually
24% monthly
12% quarterly
11% bi-annually
13% annually
Blue team success rates

Why Purple Teaming Matters
Most organizations have invested in security tools such as SIEM, EDR, XDR, email security, identity controls, cloud monitoring, and incident response platforms. Yet many still struggle to answer a difficult question:
Are these tools actually working against the attacks we are most likely to face?
A Purple Team exercise validates that answer in a controlled and collaborative way.
Where penetration testing may identify exploitable weaknesses, and red teaming may test stealth and resilience, Purple Teaming is focused on improvement. It turns attack simulation into a structured learning process for the blue team, security engineers, incident responders, and leadership.
The purpose is not to “catch” the defenders failing. The purpose is to help defenders get better.
HolistiCyber’s Purple Team Service helps organizations:
- Validate whether security controls detect real attacker techniques.
- Identify gaps in logging, alerting, correlation, and escalation.
- Improve SOC analyst skills through live, guided attack scenarios.
- Tune SIEM, EDR, XDR, and detection logic during the engagement.
- Strengthen incident response playbooks.
- Prioritize remediation based on actual business risk.
- Build confidence in the organization’s ability to detect and respond.
For executive leadership, Purple Teaming provides something especially valuable: evidence-based assurance. Instead of relying only on tool deployment status or compliance reports, leaders receive a clear view of how their organization performs against realistic attack scenarios.
The HolistiCyber Difference
Many firms can run offensive security tests. HolistiCyber’s advantage is its ability to combine elite attacker simulation with mature defensive improvement.
HolistiCyber does not approach Purple Teaming as a technical drill alone. It approaches it as a business resilience exercise.
Attacker-Point-of-View Simulation
HolistiCyber begins by thinking like the adversary. Before executing any technique, HolistiCyber analyzes the organization’s likely threat profile, external exposure, industry risks, crown-jewel assets, identity architecture, cloud footprint, business processes, and security maturity.
This allows the engagement to reflect realistic attacker behavior, such as:
- Targeting privileged identities.
- Exploiting exposed services.
- Abusing legitimate tools already present in the environment.
- Moving laterally through trusted systems.
- Attempting access to sensitive data.
- Testing exfiltration paths.
- Evading or bypassing existing controls.
- Simulating ransomware preparation behaviors without causing disruption.
This attacker mindset is critical because real adversaries do not operate according to a checklist. They adapt. They observe. They choose paths of least resistance. HolistiCyber helps organizations understand those paths before a real attacker does.
Think Like Your Adversaries
HolistiCyber’s framework goes beyond “can this technique be executed?” It asks:
- Why would an attacker choose this path?
- What business asset would they target?
- What signals should defenders see?
- Which controls should interrupt the attack?
- What would the attacker do if blocked?
- How should the blue team respond?
- What telemetry is missing?
- What must be improved now?
This mindset transforms the exercise from technical validation into a strategic defense capability.
Prioritize and Defend What Matters
A common weakness in security programs is that effort is spread evenly across assets, even though business risk is not evenly distributed.
HolistiCyber focuses on what matters most:
- Critical business applications.
- Sensitive customer or employee data.
- Financial systems.
- Intellectual property.
- Production infrastructure.
- Identity providers and privileged accounts.
- Cloud environments.
- Operational technology or data center environments, where relevant.
- Systems supporting revenue, service delivery, or regulatory obligations.
This ensures the Purple Team exercise produces business-relevant outcomes. The goal is not simply to generate findings. The goal is to improve protection around the assets that would cause the greatest harm if compromised.
Benefits for the Organization and the Blue Team
Benefits for the Organization
Validated Cyber Readiness
Security leaders often have dashboards showing tool coverage, patch status, alert volume, and compliance metrics. These are useful, but they do not fully prove readiness.
HolistiCyber’s Purple Team exercise validates whether the organization can detect and respond to realistic attacker behavior across the full attack lifecycle.
The engagement helps answer:
- Did the SOC see the activity?
- Did the right alerts fire?
- Were alerts prioritized correctly?
- Did analysts understand what was happening?
- Was escalation timely?
- Did response actions contain the simulated threat?
- Were business-critical systems protected?
- Did security tools produce useful evidence?
This gives leadership a clearer view of operational resilience.
Better Return on Security Investments
Organizations spend heavily on cybersecurity platforms, but many tools are under configured, poorly tuned, or not fully integrated into response workflows.
HolistiCyber helps clients extract greater value from existing investments by validating and improving:
- SIEM correlation rules.
- EDR detection logic.
- XDR workflows.
- SOAR playbooks.
- Identity monitoring.
- Cloud security alerts.
- Endpoint telemetry.
- Network visibility.
- Log ingestion and retention.
Instead of recommending new tools by default, HolistiCyber first helps organizations determine whether their current tools are properly configured, monitored, and operationalized.
Reduced Detection and Response Gaps
Attackers often succeed not because a company has no security tools, but because the right signals are missing, ignored, delayed, or misunderstood.
Purple Teaming identifies gaps such as:
- Missing logs from critical systems.
- Alerts that are too noisy or too vague.
- EDR coverage gaps.
- Weak identity visibility.
- Lack of lateral movement detection.
- Poor cloud audit monitoring.
- Incomplete incident response runbooks.
- Unclear escalation paths.
- Limited analyst familiarity with attacker techniques.
HolistiCyber helps close these gaps during and after the exercise.
Business-Aligned Risk Prioritization
Not all findings are equal. HolistiCyber prioritizes improvement actions based on potential business impact.
For example, a detection gap affecting a low-risk test server is not the same as a detection gap affecting privileged identity infrastructure, production databases, payment systems, or executive accounts.
HolistiCyber’s reporting connects technical findings to business risk so CISOs and executives can make informed decisions about investment, remediation, and operational improvement.
Improved Board and Executive Confidence
A well-executed Purple Team engagement gives leadership a practical, evidence-based understanding of cyber resilience.
Rather than saying, “We believe our controls are effective,” security leaders can say:
“We tested realistic adversary techniques against our critical assets. We identified detection gaps, improved response workflows, tuned our tools, and validated measurable improvements.”
That is a stronger and more defensible security narrative.
Benefits for the Blue Team
Practical, Hands-On Learning
Blue team members improve fastest when they see real attacker behavior unfold in their own environment.
During the exercise, analysts learn:
- What attacker techniques look like in logs and telemetry.
- How suspicious behavior appears across endpoint, network, identity, and cloud tools.
- How to distinguish meaningful signals from noise.
- How to investigate attack chains, not isolated alerts.
- How to escalate with better context.
- How to document and communicate findings.
This is more effective than classroom training because it happens inside the organization’s actual environment, using its real tools and processes.
Stronger Detection Engineering
Purple Teaming helps blue teams move from generic alerting to threat-informed detection.
HolistiCyber works with defenders to improve:
- Detection logic.
- Alert fidelity.
- Correlation rules.
- Threat-hunting queries.
- Use cases mapped to attacker behavior.
- Response playbooks.
- Evidence collection procedures.
- Dashboarding and reporting.
The exercise creates a repeatable detection engineering discipline: test, observe, tune, re-test, and validate.
Better Incident Response Muscle Memory
In a real incident, speed and clarity matter. Purple Team exercises help blue teams practice under realistic conditions without the uncontrolled risk of an actual breach.
The blue team practices:
- Alert triage.
- Investigation.
- Scope determination.
- Containment decisions.
- Escalation.
- Communication.
- Evidence preservation.
- Coordination with IT and infrastructure teams.
This builds confidence and reduces confusion during real incidents.
Improved Collaboration Across Teams
Cyber defense rarely belongs to the SOC alone. Identity teams, infrastructure teams, cloud teams, application owners, endpoint engineers, and business stakeholders all play a role.
HolistiCyber’s Purple Team engagement brings these groups together around a common mission: understand the attack path and strengthen the defense.
This breaks down silos and improves coordination between teams that may not normally work closely together.
Blue Team Empowerment
Traditional red team exercises can sometimes leave defenders feeling evaluated but not enabled. HolistiCyber’s Purple Team approach is different.
The blue team is not treated as the audience. It is treated as an active participant.
HolistiCyber helps defenders understand what happened, why it happened, what they could detect, what they missed, and how to improve. This creates ownership, confidence, and long-term maturity.
How HOLISTICYBER Executes the Purple Team Service
Engagement Approach
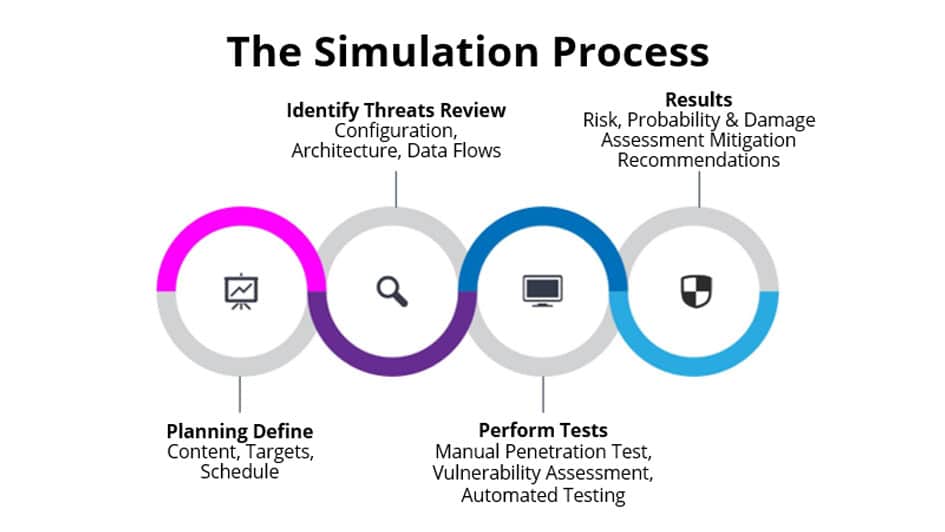
HolistiCyber executes Purple Team exercises through a structured, collaborative methodology designed to produce measurable improvement, not just a final report.
The service is typically delivered in six phases:
Phase 1: Discovery and Scoping
HolistiCyber begins by understanding the organization’s business, technology environment, security objectives, and risk priorities.
This phase typically includes workshops with:
- CISO or security leadership.
- SOC manager.
- Incident response lead.
- Security engineering team.
- Infrastructure and endpoint teams.
- Identity and access management teams.
- Cloud security team.
- Network security team.
- Application or business system owners.
- Risk, compliance, or audit stakeholders, where relevant.
The objective is to define the scope and identify what matters most.
HolistiCyber works with the organization to determine:
- Critical assets and business processes.
- Key systems to include or exclude.
- Threat scenarios of concern.
- Rules of engagement.
- Safety boundaries.
- Operational constraints.
- Communication channels.
- Success criteria.
- Measurement approach.
This phase ensures the exercise is safe, relevant, and aligned to business priorities.
Phase 2: Threat Modeling and Scenario Design
HolistiCyber then designs realistic scenarios based on the organization’s threat landscape.
Examples may include:
- Ransomware-style intrusion simulation.
- Credential theft and privilege escalation.
- Business email compromise progression.
- Cloud account compromise.
- Insider threat simulation.
- Data exfiltration attempt.
- Lateral movement from endpoint to server environment.
- Attack against identity infrastructure.
- Compromise of a critical business application.
- Data center or hosting environment attack path, where applicable.
Scenarios are mapped to attacker tactics, techniques, and procedures. MITRE ATT&CK is commonly used by security teams as a shared knowledge base for real-world adversary tactics and techniques, and HolistiCyber aligns exercises to this type of common language so that results can be clearly understood and measured.
Each scenario includes:
- Attack objectives.
- Initial access assumptions.
- Techniques to be tested.
- Expected telemetry.
- Detection hypotheses.
- Blue team response expectations.
- Safety controls.
- Success and improvement criteria.
Phase 3: Exercise Preparation
Before execution begins, HolistiCyber coordinates closely with the organization to ensure the exercise is controlled and safe.
Preparation may include:
- Confirming approved systems and test windows.
- Establishing communication channels.
- Confirming escalation contacts.
- Reviewing legal and operational constraints.
- Validating logging sources.
- Confirming monitoring tools.
- Preparing attack simulation infrastructure.
- Defining stop conditions.
- Notifying approved stakeholders.
Depending on the engagement model, the blue team may know exactly what techniques will be tested, or they may receive limited information to simulate more realistic detection and response conditions.
HolistiCyber supports both models:
- Open-book Purple Teaming: Best for training, detection engineering, and tool tuning.
- Closed book or semi-blind Purple Teaming: Best for validating operational readiness while still allowing structured improvement.
Phase 4: Collaborative Execution
During execution, HolistiCyber’s offensive specialists simulate attacker behavior in a controlled manner.
Typical activities may include:
- Reconnaissance simulation.
- Initial access emulation.
- Execution of controlled payloads.
- Credential access simulation.
- Privilege escalation attempts.
- Lateral movement emulation.
- Persistence testing.
- Command-and-control simulation.
- Defense evasion testing.
- Controlled data access or exfiltration simulation.
The blue team monitors and responds using its normal tools and processes.
Participants from the organization may include:
- SOC Tier 1, Tier 2, and Tier 3 analysts.
- Threat hunters.
- Detection engineers.
- Incident responders.
- SIEM administrators.
- EDR/XDR administrators.
- Identity and access management engineers.
- Cloud security engineers.
- Network security engineers.
- IT infrastructure representatives.
- Application owners for in-scope systems.
- Security leadership as observers or decision-makers.
HolistiCyber facilitates the exercise so each attack step becomes a learning opportunity.
For each technique, the team reviews:
- Was the activity logged?
- Was the alert generated?
- Was the alert meaningful?
- Did the SOC identify the activity?
- How quickly was it triaged?
- Was the investigation accurate?
- Was escalation appropriate?
- Was containment possible?
- What evidence was available?
- What was missing?
Phase 5: Detection Tuning and Re-Testing
This is where Purple Teaming delivers its greatest value.
When a gap is identified, HolistiCyber works with the blue team to improve detection and response. Then the attack technique is repeated to validate whether the improvement works.
Examples of improvements may include:
- Creating new SIEM rules.
- Tuning noisy alerts.
- Improving EDR policies.
- Adding missing log sources.
- Creating threat-hunting queries.
- Enhancing dashboards.
- Improving incident response playbooks.
- Adjusting escalation procedures.
- Improving identity monitoring.
- Enhancing cloud audit visibility.
- Improving endpoint coverage.
This creates a real-time improvement loop:
Simulate → Detect → Analyze → Tune → Re-test → Validate
The organization leaves the engagement stronger than when it started.
Phase 6: Reporting and Roadmap
HolistiCyber provides a business-focused and technical report that can be used by executives, security leaders, SOC teams, and engineering teams.
Deliverables may include:
- Executive summary.
- Key risk themes.
- Attack scenario overview.
- Timeline of activity.
- Detection coverage analysis.
- MITRE ATT&CK-aligned mapping.
- Validated detections.
- Missed or weak detections.
- Telemetry gaps.
- Tool configuration recommendations.
- Incident response observations.
- Blue team performance insights.
- Prioritized remediation roadmap.
- Quick wins completed during the exercise.
- Strategic recommendations for security maturity.
The report is written to support both action and accountability. It helps leadership understand risk while giving technical teams specific steps to improve.
Why Choose HolistiCyber?
Benefits for the Organization
HolistiCyber is not simply testing whether attackers can get in. HolistiCyber is helping your organization become harder to attack, faster to detect, and better prepared to respond.
With HolistiCyber, clients gain:
- Elite offensive expertise.
- Mature defensive advisory capability.
- A proven attacker-point-of-view framework.
- Business-risk-based prioritization.
- Deep experience improving SOC and incident response maturity.
- Practical tuning of existing security investments.
- A collaborative model that strengthens internal teams.
- Clear executive reporting and actionable technical deliverables.
HolistiCyber’s Purple Team Service is ideal for organizations that want to move beyond compliance-driven security and build real cyber resilience.
The strongest security programs are not built on assumptions. They are built on validation.
HolistiCyber’s Purple Team Service helps organizations see themselves through the eyes of an adversary, understand where defenses succeed or fail, and strengthen the controls, people, and processes that protect what matters most.
By combining attacker realism with defender enablement, HolistiCyber helps organizations turn cyber defense into a measurable, repeatable, and continuously improving capability.
