Enabling CISOs to Meet The Challenge of Cyber Security Planning

By Ronen Lago As cybersecurity experts dedicated to analyzing and researching the latest threats, we at Holistic Cyber welcome initiatives like the U.S. government’s National Cybersecurity Strategy. The strategy, released publicly in March of this year, is a comprehensive plan that outlines the nation’s approach to addressing cybersecurity challenges and protecting its critical and digital […]
Does Pentesting Save You Money On Cyber Insurance Premiums?

Way back in the cyber dark ages of the early 1990s as many households were buying their first candy-colored Macintoshes and using them to play Oregon Trail and visit AOL chat rooms, many businesses started venturing into the digital realm as well by giving employees access to the new digital tools like email, ftp file […]
SolarWinds And A Controversial New Era For CISOs
The notorious SolarWinds cyber breach of 2020 is making headlines once again, and CISOs everywhere are talking about how the latest legal filings may have a lasting impact on how they do their jobs. SEC Charges SolarWinds CISO As discussed in our earlier blog, “The Rise of CISO Accountability,” the SEC previously sent notices to […]
CISO Accountability When Orgs Experience a Major Cyber Attack

Consider the following scenario: You are the CISO of a large, publicly traded company. Let’s say it’s a financial organization whose stock has hit a rough patch lately. The company experiences a major cyber attack, and you discover that the threat actors have deployed ransomware across your network and have encrypted and exfiltrated considerable amounts […]
Assessing the Current State of Geopolitics and Cybersecurity
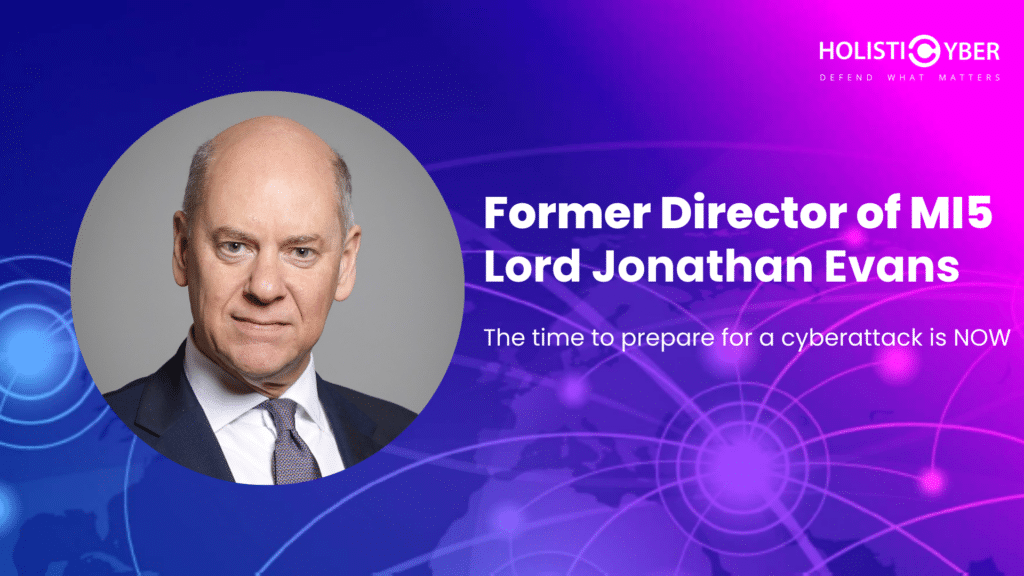
By Lord Jonathan Evans Former Director General of the British Security Service and Advisory Board Member, HolistiCyber As we pass the midpoint of a year awash with complex geopolitical and cybersecurity challenges, we should reflect on the current intersection of these realms and the implications for private organisations. In this article, I will explore the […]
Was The Killnet’s Video Cyber Threat and Attack Serious?

Major Incident or Major Yawn? In early June of this year, the cybersecurity community was shaken by a video released on Telegram and Twitter, allegedly by Pro-Russia cyber threat actors. The video, which featured a series of ominous talking heads against a dark colored background, accompanied by electronic music and an artificially generated voice, issued […]
Harnessing the Power of Adaptive Cyber Defense

“Ch-ch-ch-ch-changes Turn and face the strange” Who knew that the great David Bowie had a hidden talent as a cybersecurity expert? Clearly, his famous song intends to reveal a fundamental truth about cybersecurity planning and offer CISOs some great advice. As Bowie was unintentionally hinting, a cyber defense plan that is flexible enough to handle […]
Strengthening The Canadian Financial Sector’s Cybersecurity
Navigating the New Era of Regulations Canada is demanding its banks strengthen their cybersecurity. In response to what they are calling, “an environment that has created an urgency for enhanced regulatory guidance,” The Office of the Superintendent of Financial Institutions (OSFI) is taking decisive action to enhance cybersecurity within the banking and finance sector. […]
Why Causal AI is Crucial to Cyber Defense Planning in 2023
Recently, there’s been tremendous hype around artificial intelligence. For cybersecurity practitioners, it’s becoming increasingly important in developing a cybersecurity strategy. AI’s ability to scan millions of events in seconds while identifying anomalies and suspicious patterns is far superior to rule-based scans. It has applications in endpoint protection, securing IoT devices, cloud security, IIoT, and network […]
Prioritize Cyber Risk With Business Impact Analysis

As an industry, cybersecurity companies often talk about risk. However, we rarely take the time to explain what risk is or how it impacts organizations. It’s important to understand that risk is measured based on the negative impact it can have on the enterprise’s mission. Let’s look at a basic example: Many employees play solitaire […]
